Back Up Your Claim to Data Security
Whether you’re a technology or cloud service provider, or a collections company or contact center, trust is a crucial asset. You handle critical confidential data, from financial transactions to employee and hospital records. So your customers need to know their data is safe in your hands.
Barnes Dennig’s dedicated SOC reporting team can give your customers that verification with a SOC 2 or SOC 3 report.
Can’t watch the video? Get the transcript. Watch our SOC reporting video series on the Barnes Dennig YouTube channel.
About SOC 2 and SOC 3 reports
Both SOC 2 and SOC 3 reports provide assurance about compliance and operations. Both focus on controls related to:
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy
Which report is right for you?
First, consider what level of assurance you need to provide — and to whom.
SOC 2
SOC 2 reports:
- Contain the Security or Common Criteria and any other Trust Services Criteria (TSCs) that apply to the controls protecting your system
- Are meant for customers, prospects, and business partners who rely on your system and your control environment
There are two different categories of SOC 2 reports:
- SOC 2, Type 1 reports, which evaluate whether controls are properly designed, implemented, and documented at a specific point in time (sometimes called “SOC light”)
- SOC 2, Type 2 reports, which evaluate whether controls are properly designed, implemented, and documented over a period of time
SOC 3
SOC 3 reports:
- Consist of a high-level summary and a seal of certification
- Are meant to be shared with the general public and/or used for marketing purposes
What are the differences between a SOC 2 and a SOC 2 Plus report?
In this episode of our Ask the Experts video series, SOC Reporting practice leaders Robert Ramsay and Bryan Gayhart explain the differences between a SOC 2 report and a SOC 2+ report.
Can’t watch the video? Get the transcript.
How we prepare your SOC report
Barnes Dennig’s dedicated SOC team includes assurance, IT, and internal control professionals with years of experience preparing SOC reports for a wide range of large and small businesses. We hire, train, and cultivate IT auditors with a good bedside manner. We want this process and these reports to be as valuable as possible for you and your customers.
During a typical SOC 2 or SOC 3 examination, the team looks at:
- Physical security
- Application security
- Security administration
- Internet and infrastructure services
- IT operations, systems, and programming
- Controls over software changes
- General control environment
- Business continuity planning
- Your vendors that are key to delivering your service
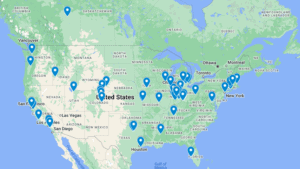
Barnes Dennig SOC Reporting Client Locations