The Gold Standard of Proof for Data Security
Payroll.
Cloud computing.
Data centers.
Document management.
What do these services have in common? If your customers outsource them to you, those customers want to know your controls are strong. And that requires independent validation.
Data security concerns are rising with the increasing use of models like Software as a Service (SaaS), Security as a Service, Platform as a Service, and Data as a Service. The pressure mounts with every high-profile data breach.
But a single System & Organization Control (SOC) report can satisfy multiple assurance requests. And a call to Barnes Dennig ensures an objective evaluation, proving the compliance of your control environment.
SOC 101
Robert Ramsay, our SOC Reporting practice leader, is a designated SOC specialist for the AICPA, which enables him to work for other firms and serve as a quality control inspector nationally.
Watch as he shares some of his insights:
Can’t watch the video? Get the transcript.
Download our free SOC reporting FAQ
Have questions about SOC reporting? We’ve got answers. Download our SOC reporting FAQ now.
Ready to go deeper?
Check out our Ask the Experts series, and the full series on SOC reporting on the Barnes Dennig YouTube channel.
Our SOC reporting services
Barnes Dennig’s SOC specialists can handle any type of assurance request you’re likely to receive, including Sarbanes-Oxley requirements, B2B, data centers, healthcare and HIPAA, banking, finance, PCI DSS, and vendor due diligence.
They do this by providing:
SOC Readiness Assessments
To ensure your management understands the reporting process, allow us to help you develop your first SOC report through a process resembling an open-book test. We call this a Readiness Assessment, and it’s one of Barnes Dennig’s signature services.
We’ll work with you on your schedule to identify new policies and procedures you may need to pass your first SOC audit. We use a simple file sharing and project management tool to:
- Assign specific items to different people
- Communicate details about open items
- Provide project status graphs with the click of a button
SOC 1 Reports
There are two different kinds of SOC 1 reports, both of which analyze a service organization’s internal controls that pertain to financial reporting.
- SOC 1, Type I – A look at whether controls are properly designed, in place, and documented as of a certain point in time.
- SOC 1, Type II – A look at whether controls are properly designed, in place, and documented across a period of time. This is the report auditors believe provides the assurance needed over the outsourcer’s finances.
SOC 2 Reports
These reports evaluate a service organization’s controls on data security, availability, processing integrity, confidentiality, and privacy.
They may also cover other established controls. The most common of these, known as SOC2+, come from HITRUST and the Cloud Security Alliance. For companies complying with HIPAA rules, the AICPA has worked closely with HITRUST to map the HITRUST Common Security Framework (CSF). The AICPA has also worked with the Cloud Security Alliance to map controls to the Cloud Controls Matrix.
| Governing Body | Controls Framework | Compliance Intent |
|---|---|---|
| AICPA | SOC 2 Security, Availability, Confidentiality, Processing Integrity and Privacy | General Third-party Vendors |
| HITRUST | HITRUST CSF | HIPAA |
| Cloud Security Alliance | Cloud Control Matrix | SaaS Vendors |
SOC 3 Reports
These simplified derivatives of SOC 2 reports may be published online for the general public. They’re offered in addition to the more detailed SOC 2 reports.
Sectors we serve
We do SOC reporting for a range of sectors, including:
- Software as a Service (SaaS)
- Data centers & payroll providers
- Billing systems
- Printing & mailing
- Collections & receivables
- Call centers & contact centers
- Business process outsourcing (BPO)
- Enterprise risk management (ERM)
- Bureau of Workers’ Compensation (BWC) processing
- Medical billing
- Cloud accounting systems & cloud data analysis
- Personally identifiable information (PII) compliance
- Health Insurance Portability and Accountability Act (HIPAA)
- Payment Card Industry Data Security Standard (PCI DSS)
- Higher Education Community Vendor Assessment Toolkit (HECVAT)
- Family Educational Rights and Privacy Act (FERPA)
- Germany’s Cloud Computing Compliance Controls Catalog (C5)
- International Standard on Assurance Engagements (ISAE) – ISAE 3000 & ISAE 3402
- National Institute of Standards and Technology (NIST) frameworks
- International Organization for Standardization (ISO) frameworks
- Health Information Trust Alliance (HITRUST)
Barnes Dennig SOC Reporting Client Locations
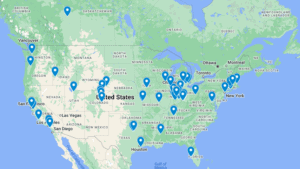
As certified public accountants (CPAs), Barnes Dennig professionals have a deep understanding of the AICPA’s SOC requirements. Our auditors’ experience stretches back before SOC reporting to Statement on Auditing Standards (SAS) 70 and SSAE 16 reporting. We’ve established and tested internal controls and IT controls for many companies like yours.
Why not make our perspective and breadth of knowledge your own?